NSA Compliant Hard Drive Destruction
NSA/CSS Specification 9-12. Digital Media Destruction for Secret, Classified, and Controlled Unclassified Information (CUI).
Degauss | Destroy | Disintegrate | Report
National Security Agency: Classified Data Destruction
The National Security Agency (NSA) has strict requirements for government contractors when destroying hard drives and other digital media. These policies and procedures are aimed at ensuring that Confidential, Classified, and Secret information cannot be recovered or accessed by unauthorized individuals after the disposal of computer hardware. Rules for NSA compliant hard drive destruction procedures can be found in NSA/CSS Specification 9-12.
NSA/CSS Specification 9-12 hard drive destruction policy includes 1) destruction methodology, 2) use of EPL approved equipment, and 3) reporting and record keeping.

Hard Drive Destruction

Hard Drive Degaussing
HPM-2. NSA/CSS EPL listed degausser erases Longitudinal Magnetic Recorded (LMR) and Perpendicular Magnetic Recorded (PMR) with a coercivity of 5000 Oersteds. Permanent magnet – 1,000+ server drives per hour.

Disintegration
Disintegrator for high security/classified data on optical media (CDs/DVDs/Blu-ray Discs) in accordance with NSA guidelines.


NSA -Classified Information Destruction
Required Destruction Equipment
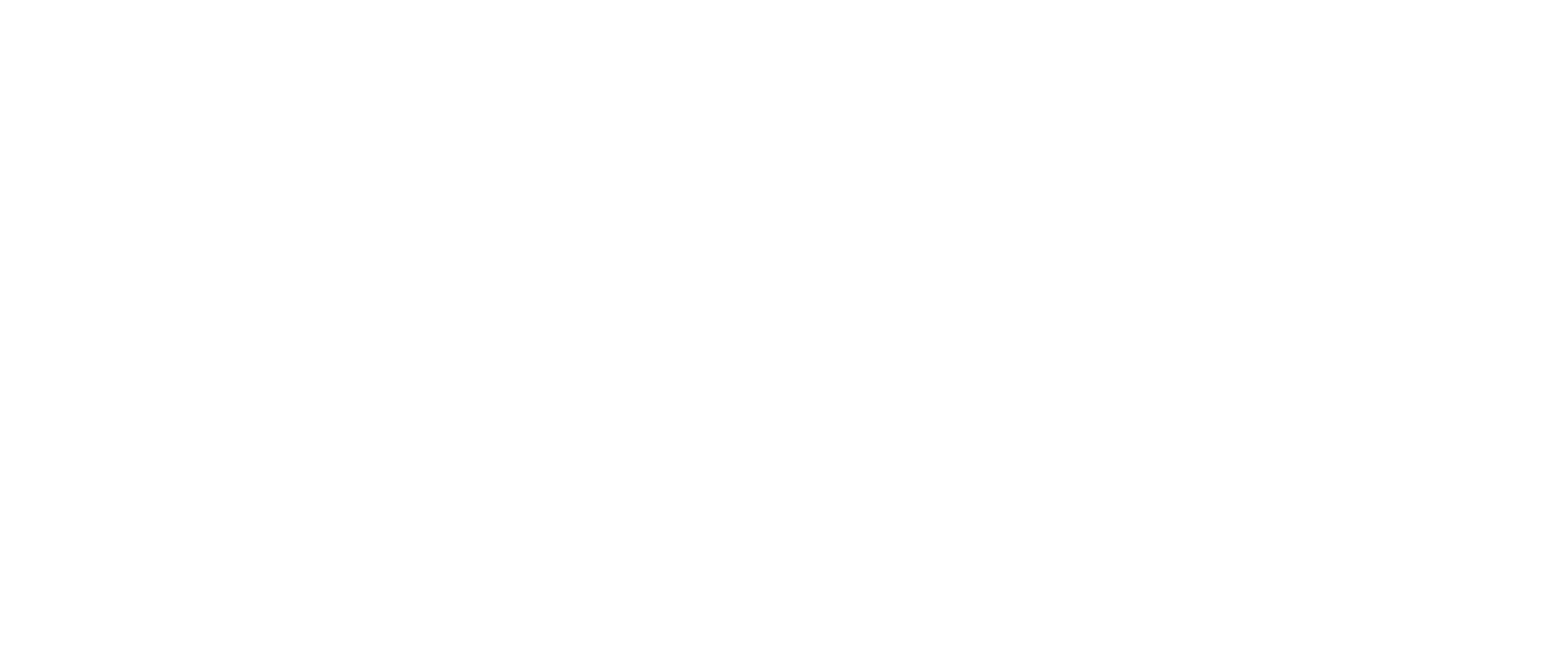
All destruction equipment (shredders, disintegrators, degaussers) must be tested and approved by the NSA. The NSA evaluates and lists acceptable products on the NSA/CSS Evaluated Products List (EPL). The type of equipment used for destruction is based on the type of digital media. For example, SSDs cannot be degaussed like a magnetic or hard disk drive.
Witness and Verification
The destruction process requires the presence of at least two authorized personnel to witness the destruction, ensuring that materials are destroyed within NSA standards.
Verification and documentation of the destruction process are crucial. This includes maintaining logs and certificates of destruction which detail the date, time, method used, and personnel involved. This document can come in the form of a Certificate of Destruction from E-Waste Security or other certified data destruction vendor.
Destruction Methods - Particle Size
Hard drives and other magnetic media need to be degaussed and destroyed. The destruction or shred size does not matter. The degauss process scrambles or erases the data and the destruction makes the media unusable. SSDs and flash media need to be disintegrated to 2mm to comply with NSA requirements.
The destruction of the hard drive consists of “physically damaging by deforming the internal platters…” The NSA/CSS Policy Manual 9-12 “Storage Device Sanitization and Destruction Manual” does not require shredding the drive to a certain size.
Audits - Inspections - Vendor Due Diligence
Use a vetted or certified data destruction vendor if your organization does not have media destruction on the EPL list.
Audits will require documentation of the equipment used. This report should include the make, model, and serial number for each machine on the EPL.
Digital Media Destruction Guidance
The National Security Agency (NSA) provides specific guidance for complying with digtal media and hard drive destruction projects. The manual entitled NSA/CSS Storage Device Sanitization Manual 9-12 details the proper methodology and equipment required for contractors and agencies. In addition, the NSA/CSS Policy 6-22 “Handling of NSA/CSS Information Storage Media” assigns responsibilities for the secure handling of all NSA/CSS information media storage These policies and manuals detail the acceptable equipment and methodology for hard drive destruction.